“Know thy enemy and know yourself” goes the ancient Chinese saying from Sun Tzu’s military opus, The Art of War. It’s a piece of wisdom that enterprises would do well to heed when dealing with the growing threat and damage that a ransomware attack can inflict on their business.
To use Tzu’s full quote – when you’re ignorant of the enemy but know yourself, your chances of winning or losing are equal; if you’re ignorant both of your enemy and of yourself, you are sure to be defeated in every battle.
This week, as part of our Cyber Security Themed Week, TechInformed will publish our exclusive Ransomware Report. In the first part of the report – which draws on expert advice from over 40 CISOs and security experts and aims to protect and prepare enterprises for ransomware attacks – our focus is firmly on the enemy’s camp: the ransomware operators.
What is ransomware?
Ransomware is a malware that encrypts an individual’s or organisation’s data and then demands payment in return for providing a decryption key. Once the data has been encrypted by ransomware, the hacker usually demands a ransom using Bitcoin or another digital currency to decrypt and regain access to their files.
The growing threat of ransomware has caused some enterprises to acquire Bitcoin solely for the purposes of attacks – although whether a ransom should ever be paid or not is something we’ll discuss in part three of this series.
Ransomware’s cost to business can be immense – according to Sophos’s 2022 State of Ransomware report, the average total cost of recovery from a ransomware attack in 2021 was $1.4 million.
The subsequent data loss can cause a business to be down for 10 days or longer, meaning factors such as product sales and business productivity are also affected. And it’s hard to quantify the kind of reputational damage a breach can cause a firm.
The dark web
So who are the hackers and how do they operate? The stereotyped image of the malevolent hoodie-wearing hacker is in urgent need of an update: digital transformation has swept through the criminal underworld – turning a cottage industry into a multimillion-dollar criminal racket with software-as-a-service offerings similar to most legitimate tech businesses.
Conversely, because it’s never been easier for the have-a-go-cyber-crim to don a hoodie and inflict some serious damage, to some extent this stereotype persists – albeit one that now operates within a much more complex framework.
According to Roger Grimes, a data driven defence evangelist at KnowBe4, today’s ransomware criminals run the gamut from lone individuals (a practicing cardiologist was recently arrested for selling ransomware) to criminal gangs, cartels and nation state sponsored attackers.
Most operate via the dark web – that encrypted alcove of the internet which is not indexed by search engines and requires a specific configuration or authorisation to access – usually a peer-to-peer connection or by using an overlay network such as the Tor browser.
While this anonymous part of the internet can be used by people who require privacy for legal reasons – the exchange of proprietary business data or for political activism for instance – these networks have contributed to the dark web’s reputation as a hotbed for criminal activity.
Technology, training and ransomware-as-a-service kits (or all three bundled in together) can be accessed cheaply and anonymously on the dark web.
A recent HP Wolf Security Report analysed 35m hidden dark web sites, noting that cybercrime is being supercharged through ‘plug and play’ malware kits that are making it “easier than ever” to launch an attack. As a result, only 2-to-3% of today’s criminals are high coders.
Tools of the trade
On the dark web marketplace, exploit kits, remote desktop protocol (RSP) server access, and attacks that flood a server with internet traffic to block paying customers to have access (DDoS-for-hire) are the most in-demand cyber products and services on marketplaces, according to Smith from S-RM.
A data-stealing Trojan is one of the most popular tools, which can steal passwords, cookies and credit card information, can be bought for as a little as $50-150, according to Smith.
“A ransomware kit can cost from $40 to several thousand dollars a month, depending on the malware strain and whether affiliates share profits with operators,” says Smith, adding that “there are also sophisticated malware sellers who offer customers free updates, customer support, and in-depth tutorials.”
Additionally, some RaaS groups provide tools and tutorials directly to their affiliates and will trust to receive a split profit of the attack.
Whilst cybercriminals will purchase tools, code, and tutorials to hack into organisations, they can also often simply purchase verified credentials for compromised organisations which could be used as an access point to the organisations network.
A recent example, provided by Searchlight Security, found a user selling credentials relating to a UK-based energy company.
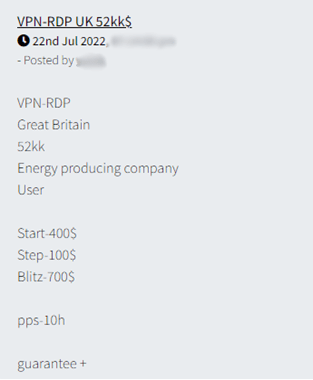
A user selling credentials relating to a UK-based energy company, Searchlight Security
And it has also observed credentials from target organisations being sold in dark web auctions for as much as $40K.
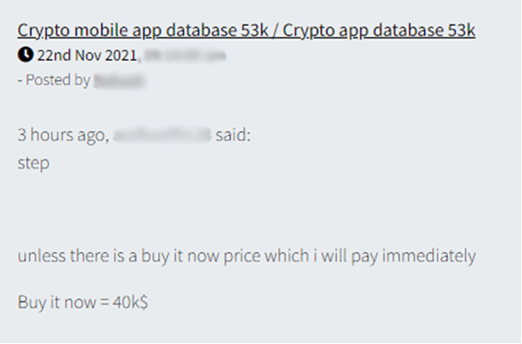
Credentials from target organisations being sold on the dark web, Searchlight Security
The ubiquity of RaaS
Rather than one individual or one large gang, behind each ransomware attack that happens today, there’s likely to be highly orchestrated business that comprises of a few different types of threat actors.
“Ransomware groups don’t take control of each and every aspect of the operation now, they outsource parts to threat actors that are not part of their core group,” explains Yuval Wollman, chief cyber officer and president at CyberProof – a UST company.
Ransomware gangs are adopting all the core elements of legitimate businesses – including defined staff roles according to Robert Fitzsimons, a threat intelligence engineer at Searchlight Security.
Different roles up for outsourcing parts of a ransomware attack include initial access to the organisation; lateral movement through the network and privilege escalation; data exfiltration and clean-up as well as developers to work on bugs or new features for the malware.
Fitzsimons adds that these functions might be coupled with “middle management roles, criminals in charge of the PR campaigns to promote the attack, and a negotiator to handle the communication with the victim”.
He adds: “The most sophisticated groups manage internal user interfaces and messaging channels so that they can rapidly fire off multiple attacks and thus increase the chances of securing a ransom payment from one of the victims.”
The evolution of distinct roles with a ransomware attack has been shaped by the emergence of the Ransomware as a Service model.
RaaS is growing for the very same reasons that software-as-a-service is growing – convenience and access to application functionality without having to install, maintain or even understand the technology itself in order to to use it, alongside the advantages brought by scale.
As Alexandra Willsher, senior sales engineer at cybersecurity company Forcepoint notes: “Criminals now build once and resell many times over.”

Alexandra Willsher, senior sales engineer at Forcepoint
RaaS also affords criminals the luxury of anonymity: hackers can rotate between renting numerous strains for malware, making it harder to pinpoint who they are as there’s no longer a signature methodology.
Prolific Ransomware-as-a-Service (RaaS) operators include Lockbit, Blackcat, Hive, Clop and – until recently – Conti.
The latter Russian-based operator – whose victims have ranged from clothes retailers such as Fat Face to the government of Costa Rica – apparently wound down in May this year, although is reported to be rebranding as several new ransomware groups.
Conti’s decision to regroup follows a huge leak of internal documents that revealed details about the inner workings of one of the world’s biggest ransomware groups.
The messages revealed that Conti operated much like a regular company, with salaried workers, annual leave, bonuses, performance reviews and even employees of the month.
Whichever the operator, what RaaS has served to do is to lower the entry point for other individuals or groups to perform ransomware attacks, says Jason Illingworth, principal analyst at NormCyber.
“By using tools developed and sold by the main groups, they’re able to take a portion of the paid ransom, allowing more cybercriminals to launch ransomware attacks and increasing the scope of companies targeted. The main groups can focus more time on developing new tools while those that have paid for the tools carry out the attacks,” Illingworth adds.

Jason Illingworth, principal analyst at NormCyber
It’s a trade-off that suits everyone: RaaS also poses less of a risk for malware authors, as they’re not the ones carrying out the actual attacks while, Steven Furnell, IEEE senior member and professor of cyber security at the University of Nottingham notes, by using RaaS , would be cybercriminals are also paying for a tried and tested malware – rather than risk of devising their own solution.
The Big Tech-level of efficiency with which these organisations are run, helps explain the reason why ransomware attacks are currently soaring. And to hyper charge operations further, there’s also been a trend over the last two years for collaboration and partnerships between different ransomware operators: sharing knowledge, stolen data, leaked information and other resources to exhort victims, enhance their capabilities and improve their success rate.
One of the most notable cartels over the last two years has been the Maze-Ragnar Locker- SunCrypt cartel. According to reports, Maze grew so big that it couldn’t handle all available field operations and invited other operations such as SunCrypt into the fold on a revenue share basis to help handle attacks.
Forums
Platforms through which ransomware tools and newly discovered vulnerabilities in software are discussed, include Exploit, Dread, Nulled and Cracked. Others, such as Russian speaking forum XSS have banned all topics relating to ransomware in order not to draw attention to themselves.
This followed a raid on RaidForums – a popular English language forum which was taken down by law enforcement agencies in April.
Because forums have now become a police target – most active and well-known RaaS gangs communicate directly via their leak sites on the dark web, according to Daniel Dos Santos, head of security research at Forescout.
The dark web is not the only place where ransomware is traded, however. According to Hugh Raynor, senior cybersecurity consultant at SureCloud, apps such as Telegram and Signal are also being used to trade ransomware “which is perhaps not surprising given their end-to-end encryption”.

Hugh Raynor, senior cybersecurity consultant at SureCloud
There have also been multiple reports of malware being traded on the text and chat app Discord – which lacks encryption and is said to actively work with the authorities. However, Raynor explains: “The ease of marketing Discord servers to users of the platform and the huge market of potential buyers for these services has clearly tempted some groups.”
As a case in point, researchers at cyber firm Avast recently discovered an online community of children using dedicated Discord servers to build, exchange and sell malware. Criminal groups lure in by advertising access to different malware builders and toolkits that can be used to code malware without much technical experience.
But how much damage can inexperienced “script kiddies” inflict by purchasing malware or software tooling from forums and non-discriminately targeting various systems and organisations to learn and ‘play around’ with their tools?
Paul Baird, chief technical security officer UK at Qualys puts it this way: “You could describe an experienced hacker as a smart weapon with precision accuracy, while the novice hacker is like cluster ordinance that creates unimaginable damage over a wide area without any thought for the future.”
How do hackers access networks? This is Part 1 of our Ransomware Special Report. To read the other parts, please click on the links below:
Part 2: How hackers find their way in